Security certificates are critical tools for designing cybersecure automation systems, and they're easier to set up on your groov devices than you might think.
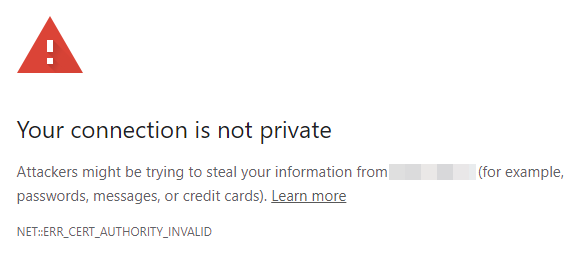
Have you ever seen a warning message from your browser telling you a connection is untrusted and asking if you want to proceed anyway? If you're connecting to groov Manage, then the connection this message refers to is actually your groov EPIC or RIO!
But what if I told you that in a few simple steps you can prove to browsers and other connected systems that network communications to your groov devices are secure, encrypted, and protecting your automation assets?
Security certificates are a standard mechanism used across networked systems like the internet for proving the identity of connected endpoints, establishing chains of trust between them, and encrypting all traffic using Transport Layer Security (TLS).
After properly creating certificates on your groov devices, you’ll see that trusted padlock appear in your browser’s address bar when logging into groov EPIC or RIO, just like when you log into your bank account. Let’s demystify this so you can set up this secure connection.
Security mechanisms in groov devices
Many industrial automation devices and legacy PLCs don't have the ability to create secure, encrypted connections, and they may be vulnerable to man-in-the-middle attacks on a local area network (LAN). Adding a groov EPIC or RIO to your system can add these cybersecurity tools to your automation systems:
- User authentication to prevent unauthorized access
- Fully configurable firewall to block unwanted incoming traffic
- Network zoning to separate OT networks from IT networks and protect unsecured legacy PLCs and devices
- Network conduits to reach protected PLCs and devices securely (EPIC only)
- Data services to transmit OT data securely
- SSL/TLS encryption with built-in certificate management (this is how we get that padlock!)
TLS encryption establishes secure communication between the groov device’s internal web applications like groov Manage, groov View, and Node-RED, and web browsers, servers, and cloud services. To learn more about the basics of SSL and TLS encryption, there’s a great explanation in the OptoBlog article Understanding SSL/TLS and HTTPS.
Two types of certificates
Let’s talk about two types of SSL certificates. Which you use depends on the scope of communication that your groov device participates in:
Self-signed certificate- The groov device's identity is verified by you.
- Ideal for networks with few users, not out on the internet.
- A Certificate Authority is an organization that signs your groov device's server certificate, confirming its identity to the many web browsers, devices, and cloud services that connect to it.
- Permits many users, software, and devices to access a groov device securely.
- Allows secure, encrypted access to a groov device over any network, including the Internet.
For this article, we’ll stick to the simpler, self-signed certificate.
How to create and install your certificates
These are the basic steps to secure communications with an SSL certificate on your groov device:
- Log into your groov device with an admin account.
- Choose your device's hostname, and be sure the device time is set properly.
- Create a server certificate for the groov device.
- Download the public client certificate for that server certificate.
- Install the client certificate on PCs and mobile devices whose browsers will connect to the groov device.
Let’s take a closer look at each step.
1. Login: Your groov EPIC or RIO may have more than one user account configured. To complete the rest of this procedure, make sure you log in with an account that has administrator privileges.
2. Configure device settings
- Navigate to the Network settings page, and choose a memorable hostname. You may use the default hostname if you wish, but the hostname is a key part of the certificate.
- Next, navigate to the Time settings page, and be sure to set the correct Time Zone for your EPIC or RIO.
3. Generate a server certificate
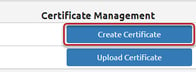
- Go to your Security settings page, then Server SSL.

- From here, click on Create Certificate.
- Fill in the requested information, mostly specific to your organization. For the Expiration (Days), it’s recommended you enter 3650 (10 years). Note this length of time is usually only valid for self-signed certificates.
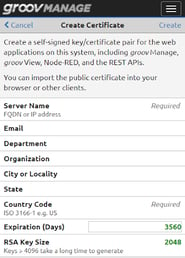 For more about these fields, see the groov EPIC User’s Guide, Chapter 6, "Creating a Self-Signed Certificate."
For more about these fields, see the groov EPIC User’s Guide, Chapter 6, "Creating a Self-Signed Certificate."
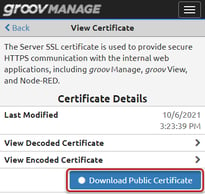
4. Generate a client certificate: After creating the server certificate, create the client public certificate by clicking Download Public Certificate.
5. Install the client certificate on connected devices: You’ll be installing the self-signed public certificate file with the .pem extension.
- If you have administrator access on your computer, you'll install the public certificate into your operating system's certificate trust store.
- If you don't have administrator access, you can alternatively install the public certificate in your favorite browser's trust store. Since there are several browsers to choose from (Chrome, Firefox, etc.), the details to install the client public certificate will vary. Pick your browser (my favorite is Chrome), and refer to the instructions in the groov EPIC User’s Guide, or on the Opto 22 Developer web site.
- Reboot your computer and log back into your groov device. This time, you’ll see the padlock in the URL field!
Conclusion
You did it! You've now established secure, encrypted communications to your groov EPIC or RIO! Someone told me it was a wonderful feeling to see the padlock in your URL browser when logging into your groov EPIC–-they were right! No-man-in-the-middle is going to get between you and your secure industrial application.
For more Cybersecurity resources, check out Resources for Cybersecurity in Automation and IIoT Applications.
