Learn how setting up VPN (virtual private network) configurations can help you securely connect to your remote devices.
In our latest video VPN configuration on groov devices using OpenVPN, you'll get a breakdown of the high-level configuration of VPNs and also a detailed walkthrough of the process.
But first, in this blog post, let's discuss the pain of secure remote connectivity and the gains that setting up a VPN can bring.
Read More
Topics:
groov EPIC,
cybersecurity,
EPIC Security,
OpenVPN
Follow along with the 4th installment of the groov Manage video and blog series as we focus on the Security button in the groov Manage menu.
This week brings you the fourth installment of walking through the groov Manage menu options found on a groov EPIC. In case you missed it, you might want to catch up on the previous three menu options we've covered so far: Accounts, Network, and System. Now, you'll be ready to dive into the Security features.
Watch groov Manage: Security.
Read More
Topics:
Videos,
groov EPIC,
groov Manage,
cybersecurity,
EPIC Security,
groov Manage series
Security certificates are critical tools for designing cybersecure automation systems, and they're easier to set up on your groov devices than you might think.
Have you ever seen a warning message from your browser telling you a connection is untrusted and asking if you want to proceed anyway? If you're connecting to groov Manage, then the connection this message refers to is actually your groov EPIC or RIO!
But what if I told you that in a few simple steps you can prove to browsers and other connected systems that network communications to your groov devices are secure, encrypted, and protecting your automation assets?
Read More
Topics:
groov EPIC,
cybersecurity,
EPIC Security
Watch and learn what it means to have a secure industrial controls system.
Industrial automation has long been known to carry cybersecurity vulnerabilities at the levels of both technology and practice. Legacy PLCs weren’t designed for connections to untrusted LANs or the internet, and the old password-on-a-sticky-note security policy just doesn’t cut it anymore. So, what's the solution?
Read More
Topics:
groov EPIC,
cybersecurity,
EPIC Security
Las mejores prácticas para el groov EPIC y la ciberseguridad
Habrá oído de ataques informáticos y cómo han afectado a empresas grandes y chicas. Sus sistemas o los de sus clientes trabajan bien, pero habrá más que se puede hacer para proteger esos sistemas? Hay estratégias de seguridad que puede incorporar a sus sistemas existentes.
Read More
Topics:
cybersecurity,
EPIC Security
The recording of Opto 22's live product demo from the 2021 Ignition Community Conference is now available.
Were you able to attend Inductive Automation's annual Ignition Community Conference (ICC) last week? This two-day virtual event featured developer panel discussions, case studies of real-world Ignition projects, the annual build-a-thon, as well as several exhibitor demo sessions.
Opto 22's presentation demonstrated the power of Ignition on our groov EPIC and RIO platforms, and the recorded webinar is now available for on-demand viewing.
Read More
Topics:
groov EPIC,
EPIC Security,
Ignition Community Conference,
webinar
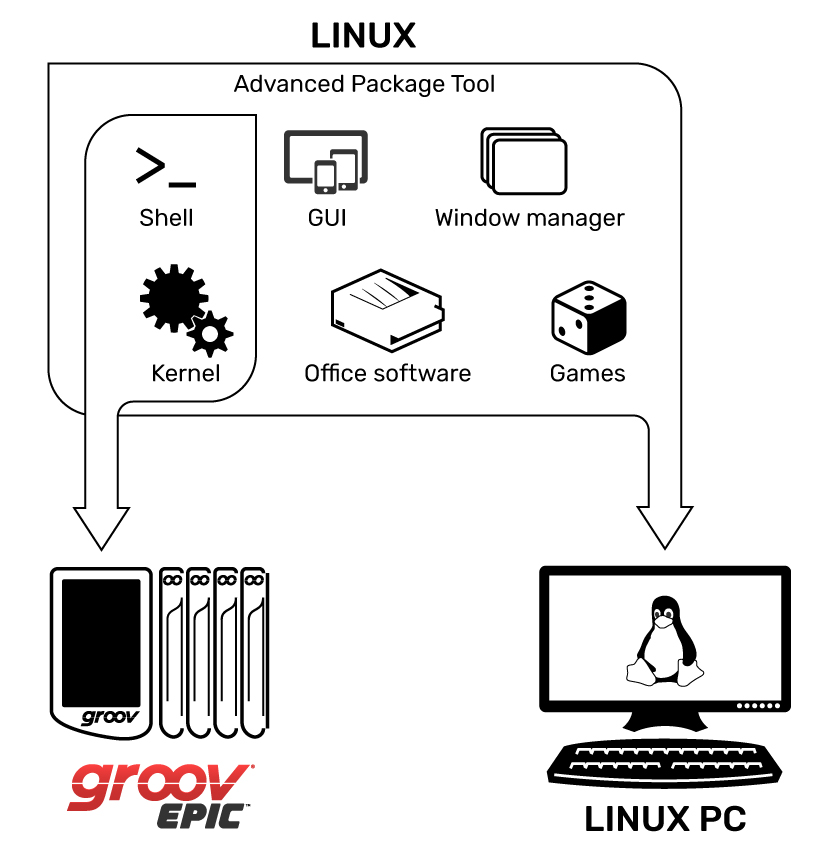
The OS, or operating system, of groov EPIC is very different from traditional controllers. Instead of a proprietary OS, EPIC uses an open-source Linux® operating system.
From a security standpoint, an “open source” OS sounds scary. But in many ways it is more secure than a closed-source one, especially a well-known and often-attacked OS such as Microsoft® Windows®.
Read More
Topics:
EPIC,
groov EPIC,
EPIC Security,
Linux,
secure shell,
ssh,
EPIC Security Series
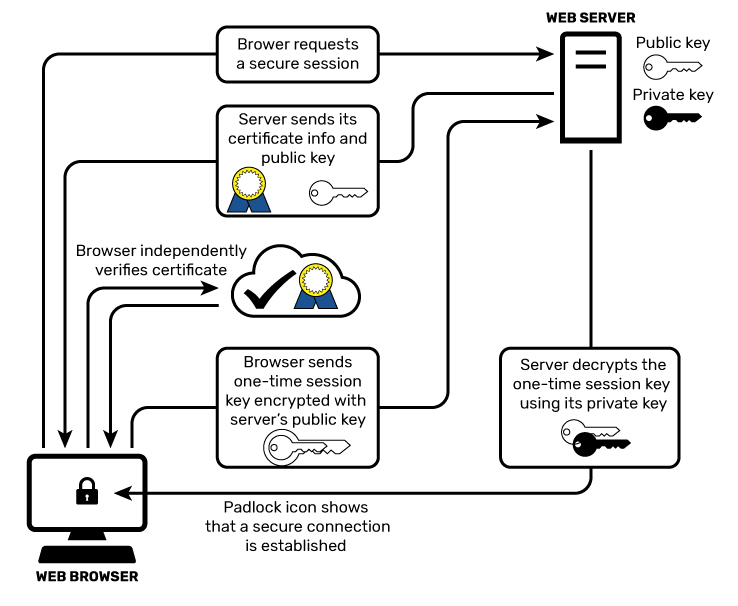
Go on, admit it. At some point in your life you've written down a password on a piece of paper in clear text. Anybody walking by can simply glance at your note, and they'll know what your password is.
No, you have never done that? Excellent.
But if you've ever used your web browser to log into a website over the web, and entered sensitive information like your password without encryption, you've effectively transmitted that information through the internet for all to see, almost like writing it on paper and showing it around.
Whoa.
Read More
Topics:
Security,
IIoT,
groov EPIC,
cybersecurity,
EPIC Security,
encryption,
EPIC Security Series
In this blog post, let’s take a closer look at user accounts on the groov EPIC system, and how you can improve your system security by giving users and services fine-grained access to applications running on EPIC. In other words, make sure each person or service has only the access they really need and nothing more.
But before we get deep into user accounts, let’s first discuss user account credentials. Take a moment and ask yourself the following questions:
- Do you use the same password for multiple accounts?
- Do you use a mix of punctuation and capital letters in your passwords?
- Do you use long phrases as your passwords?
Read More
Topics:
Security,
groov View,
groov EPIC,
groov Manage,
cybersecurity,
EPIC Security,
User Accounts,
EPIC Security Series
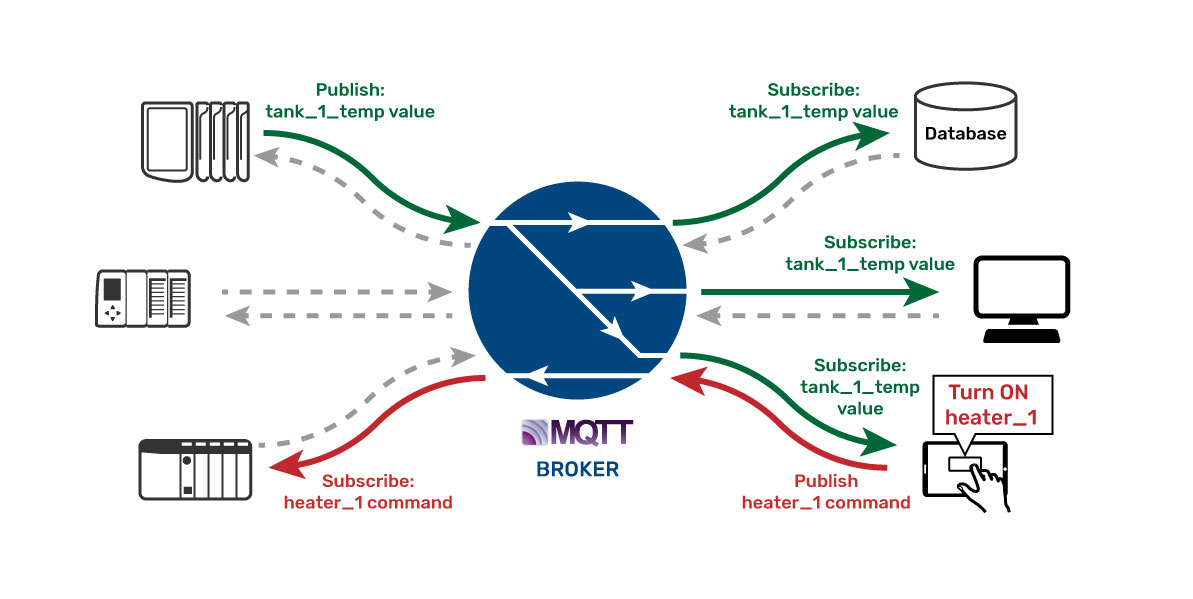
The story goes that a valve manufacturer wanted to have their networked smart valves certified for use in a nuclear reactor plant. The smart valve could report all sorts of critical data points to a database system and also be controlled by that SCADA system in the plant. But to get it certified for use, the smart valve had to undergo a rigorous security audit by the information technology (IT) department at the plant.
Read More
Topics:
Security,
MQTT,
groov EPIC,
cybersecurity,
firewall,
EPIC Security,
EPIC Security Series