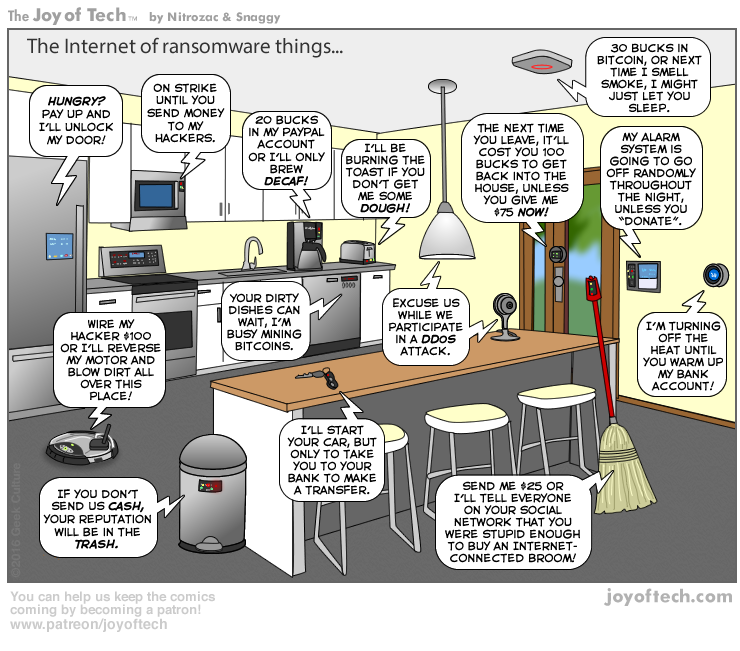
The image below still cracks me up. The captions for each of the devices are hilarious.
But in truth, ransomware is a pretty scary subject, especially when you think of it in the context of industrial technology and applications. And there’ve been quite a few unnerving stories about ransomware hacks in industrial applications lately.
One attack that comes to mind had the potential to affect thousands of victims. It happened in March of 2016. It was a story that didn’t get a lot of coverage but still should serve as a warning to all industrial engineers.
According to the Las Vegas Review Journal, the Clark County Water Reclamation District was hit with a cyberattack, possibly ransomware. “Multiple sources told the Review-Journal that the Clark County Water Reclamation District’s computer system was breached and that the hackers demanded a ransom.
“The ransom amount and whether the county paid the hackers is unclear. The county has a cyber liability policy, which covers cyber extortion. However, the water reclamation district was not covered under that policy. It is unknown at this time if the district has its own policy.”
The FBI was called in to investigate and declined to comment on the situation. The key takeaway from this story is to make sure you’re covered under a cyber liability policy and that the coverage includes cyber extortion, which seems to be all the rage lately with hackers.
According to FireEye.com, “Ransomware is malware that typically enables cyber extortion for financial gain. Criminals can hide links to ransomware in seemingly normal emails or web pages. Once activated, ransomware prevents users from interacting with their files, applications, or systems until a ransom is paid, typically in the form of an anonymous currency such as Bitcoin.
“Ransomware is a serious and growing cyber threat that often affects individuals and has recently made headlines for broader attacks on businesses. Payment demands vary based on targeted organizations and can range from hundreds to millions of dollars.
“Once infected, a victim has little recourse. If they do not pay the ransom, they suffer business down time, loss of sensitive information, or any other penalty specified by the attacker. And even when they do pay the ransom, they remain vulnerable to attack from the same attacker or a new one, and reward attackers for their successful tactics. Usually, if you have to choose whether to pay a cyber ransom, it’s too late.”
So how do you avoid ransomware affecting your industrial assets? Or your PLC and PACs getting hacked? What about your industrial wireless network? Start by getting a handle on your cyber security policies and strategy.
You can find out more about cyber security from Opto 22 in a 6-part blog series at the link below. If you haven’t changed your passwords recently, or don’t have a password policy protecting your industrial systems—please...please...read the Do you know enough about cyber security? blog series from Ben Orchard.

